Mitigating arbitrary native code execution in Microsoft Edge
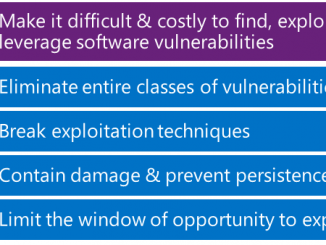
Mitigating arbitrary native code execution in Microsoft Edge Some of the most important security features in modern web browsers are those that you never actually see as you browse the web. These security features work behind the scenes to protect you from browser-based vulnerabilities that could be abused by hackers to compromise your device or personal data. In previous blog posts and presentations, we described some of the recent improvements that have been made to Windows 10 and Microsoft Edge in this space. Today we’re kicking off a two-part blog post that describes our vulnerability mitigation strategy and provides a technical deep-dive into some of the major security improvements that are coming to Microsoft Edge in the Creators Update of Windows 10. Framing our Vulnerability Mitigation Strategy Before we dive in, it may help to start with an overview of [ more… ]